68% of breaches involve a human element
CyberInsights #138 - Insights from the Verizon Data Breach Investigation Report 2024
This edition focuses on the Verizon DBIR alone. You will find a temporary change in the format of the newsletter for this edition.
The Verizon DBIR for 2024 is out. The findings are eye opening as always.
The report gets better and better each year.
Just look at the first two pages of the report and you will understand the effort and depth that Verizon goes into to publish there annual Data Breach Investigation Report. Download the report from here [LINK]
The horizontal line (opening in the door) represents the “ways in” for an attacker and the vertical line (shadow) represents the pathways. A brilliant representation.
Hoomans and their mistakes
The report starts off with the not-so-startling fact that 68% of data breaches involved a human element. Here, the human element refers to breaches that could have been prevented by proper training and awareness - not malicious insiders and ‘privilege misuse’.
By separating the honest mistakes from the malicious ones, we can establish how the impact of awareness reduces the possibility of data breach.
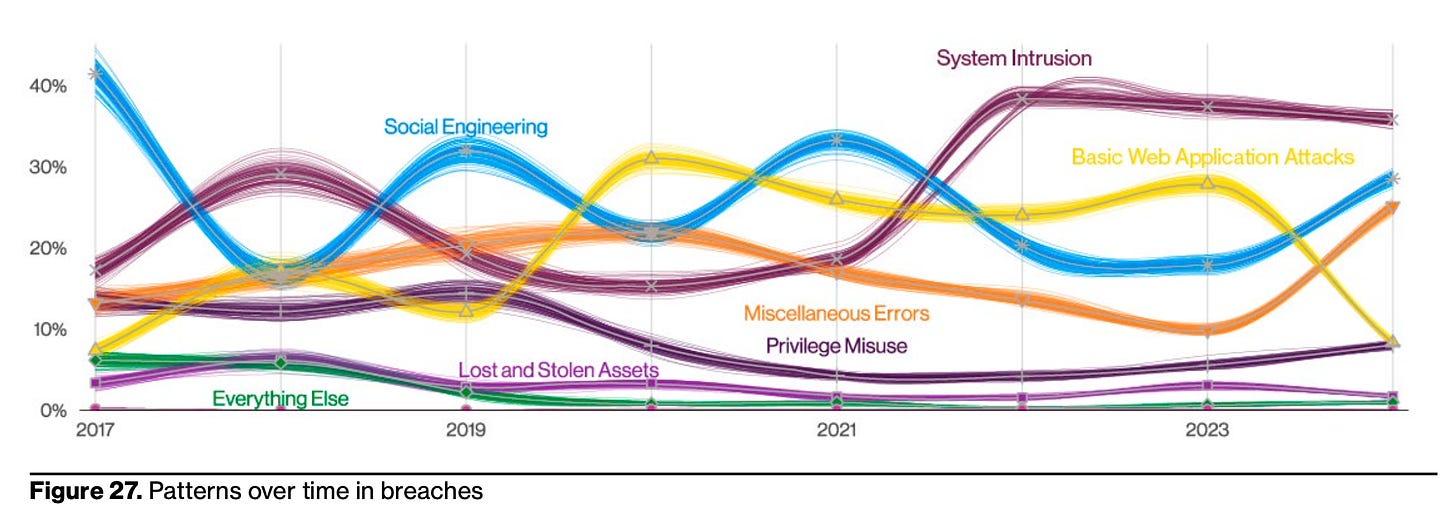
How have breaches changed over the years?
Social Engineering
Social engineering has a cyclic pattern - almost like a sine wave. The most likely reading of this is that attackers come up with new methods of social engineering, it rises, people figure it out, it reduces and the attacker comes up with a new way.
System Intrusion
After a big spike in 2021-22, system intrusion has stabilised. This is probably after the log4j and the MOVEit incidents.
Basic Web application attacks
Can you see the drop in basic web application attacks? Are we better at creating secure web apps now? I believe so. All the secure coding training and the integrated security tools in IDEs are helping us build more secure web apps.
Miscellaneous Errors
There is a sudden big spike in miscellaneous errors.
When you read the report, you see that 50% of the miscellaneous errors have something called ‘Misdelivery’ - something was sent to a wrong recipient.
Industries
The industry wise break up is an essential component of the report. This year, the industries with the largest number of breaches were:
Education
Professional (services)
Healthcare
Finance
Public Administration
There is a lot more information in this report.
Every cyber professional should read it. Download it today and read it. Discuss it with your peers. Try to figure out trends.
Cybersecurity professionals can get data for attack vector probabilities.
Cyber Underwriters can get loads of data for their underwriting process. In fact, we use the DBIR as a key input in our cyber underwriting tool CRUX. The data will give you a broad idea of key industries and risks to consider.
Cybersecurity trainers will know what type of incidents to focus on in their next round of trainings.
There is something in it for everyone!
P.S. If you want to know about DBIR 2023, read this post: