A supply chain attack of massive proportions | The world's largest money mover down for 3 days
Exploding Pagers of the Hezbollah || A money transfer site's cyber incident and the importance of BCP
Thousands of pagers exploded in a suspected coordinated attack killing 12 and injuring thousands
The Mind Boggling scale of a supply chain attack, most likely by a nation state…

It’s a supply chain attack of epic proportions.
On the 17th of September, thousand of pagers belonging to the Hezbollah exploded in a series of blasts coordinated over one hour.
It’s a cyber attack that involves taking over (or even setting up) a hardware manufacturing supply chain. It’s widely suspected that Israel is behind the attacks, but no one has claimed responsibility yet.
Who’s susceptible to the attack vector
Supply chain attacks range from the mundane editing of open source software to insert malicious code to coordinated exploding pagers. Every organisation that has a supply chain is vulnerable. The level of risk, depends on the impact a compromised supply chain might cause.
State level actors are most at risk as the consequences are the highest. Nations have stopped sourcing hardware components from countries that they do not trust. US does not buy from Huawei anymore. India has banned many China based apps.
In the corporate world, supply chain attacks can lead to large scale data breaches. Think MoveIT.
Hacktivists have often poisoned PyPi libraries.
Supply chain attacks are the fastest rising attack vectors
Take Action:
Have a strong and robust Third Party Risk Management Program (TPRM). It is important to classify all your suppliers into categories, based on the criticality of the services they provide and the impact if their confidentiality, integrity or availability is breached.
If you are a high risk organisation, then it’s not sufficient to do an immediate supplier assessment. You should consider deep dives. For example, if you are procuring cell phones from a third party, make sure that the chips that the third party procures are safe.
Implement a robust Risk Management Framework that considers all your supply chain elements - from a strong SBOM to a hardware supply chain (down to the chip manufacturer level, should it be required)
Moneygram’s ‘Cybersecurity Incident’
Systems are offline for the past 3 days.
Moneygram has not been able to move money. Since Saturday.
On Sunday, Moneygram tweeted that they have faced a network outage.
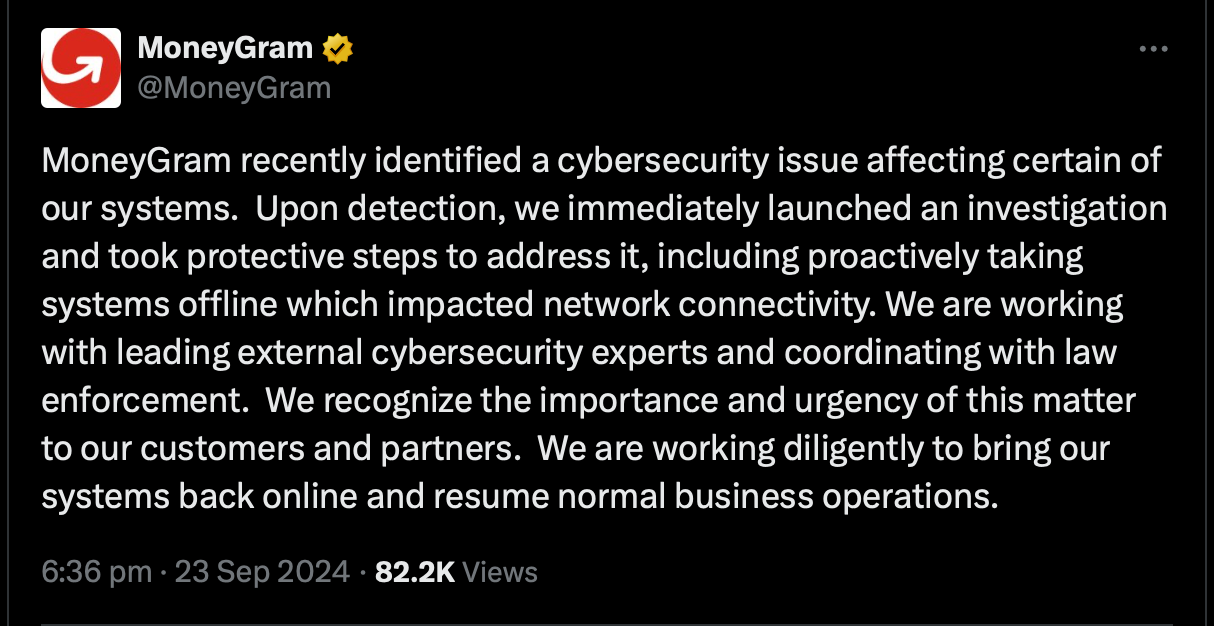
Then on Monday, they tweeted about a cybersecurity incident.
Then, on Tuesday, while systems continued to be down, they tweeted this:
All this brings into question the business continuity planning skills of MoneyGram. Did they have a BCP in place? What was their RTO? How many of their customers will move over to another service provider and never move back?
Take Action:
Let this serve as an indicator to the importance of a good BCP. Implement a strong system. Get an ISO 22301 certificate if it takes that to keep your systems on the straight and narrow.
For Cybersecurity Professionals:
Review your existing BCP.
Do table top exercises of dealing with outage. I have found that leadership teams abhor table-top exercises. They feel that these exercise add no value. They approach it with disdain and a burning desire to get it done quickly. “We have no time to discuss all this. When a crisis comes, we know what to do. We did not become the leadership team for nothing.” But, almost always, the table top exercise exposes major gaps that leaves the leadership wide eyed and open mouthed. “Why do we not have a backup link?” “Sir, you never approved the budget. It’s on your table for the last 6 months.”
Clearly communicate your RTOs and RPOs to your business teams and functions.
For Cyber Insurance Professionals:
Always ask for recovery time and sub-limit the Business Interruption to a proportion that covers only up to the recovery time.
Check the scope and coverage of the BCP. If it is only the tech teams, you know that an outage will be a rough one. Raise your premiums.
Ask how many tests of the BCP are conducted and how many scenarios are tested. Calibrate your risk scoring based on the response.
Remember that BI losses in cyber are among the most unpredictable. Take proper care.