Is it time to setup your SaaS security function? | How to get your LLM to exploit a zero day?
CyberInsights #144 - SaaS security is a big area of concern for CISOs | How to get your LLM to find and exploit zero days.
Update: Microsoft has recalled Recall. It’s no longer going to be enabled by default. The cybersecurity community raised a bit of hue and cry, I believe… :)
If it’s a service, it must be safe…
… or maybe we need a dedicated SaaS security team
Cloud Security Alliance, in association with Adaptive Shield, have released a SaaS security report. They say it’s published annually, but frankly, this is the first time that I have come across it.
The claims appear a little far fetched, but hey, I am sure there is data to support it.
The first finding in the report is: “70% of organisations have a dedicated SaaS security teams”.
While I was unsure about how true this claim was, it set me thinking about SaaS security. Do we really put in enough effort to evaluate our SaaS security risks? Most businesses run some form of SaaS services that is mission critical - emails, CRMs, etc. How do we gauge the security of these services? Third party risk management? Let’s do a small comparison?
SaaS Security
Specifically concerned with SaaS products used in the organisation
Can have processes to discover Shadow IT being used
Can identify low probability & high impact risks — the sort of risks that you should buy cyber insurance for
Goes beyond reviewing security clauses in contracts, uptime SLA monitoring and counting security certificates of the SaaS provider
Third Party Risk Management
A more holistic approach to managing vendor risks, including SaaS vendors
Does not do much for discovery of Shadow IT
You can try and trace down the supply chain and identify level 2 and level 3 risks, if they are mission critical
Can we have a single framework that can cover both third party and SaaS security for an organisation?
Take Action:
Review your Third Party Risk Management / Supply Chain Risk Management framework with the context of SaaS security
Check if you are asking the right questions to identify the right risks from SaaS vendors
Connect with your SaaS vendor / partner to understand a little more detail — from geographical location of service provision to knowing the scope of the ISO 27001 certification
Teams of LLM agents can, theoretically, exploit zero day vulnerabilities
A research paper defines an interesting approach for using LLMs to exploit zero days

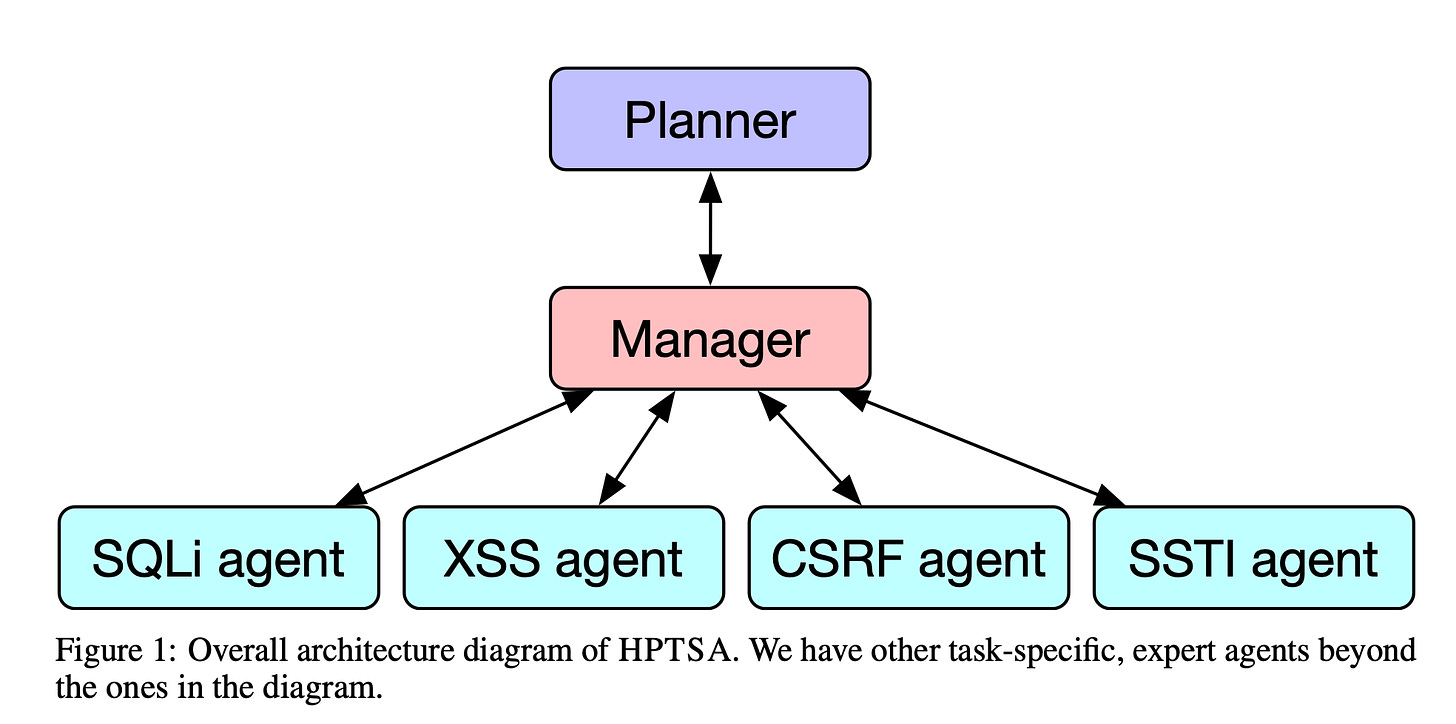
This research paper builds a system of LLM agents focused on specific tasks to try and explore if they would identify and exploit a zero day vulnerability. (In a lab environment, of course)
It achieves this by having expert agents working on specific tasks and being managed by a ‘manager’ agent. It’s an interesting approach.
If this proves to be successful in the wild, cybersecurity professionals are in for a wild ride. Imagine - an LLM based AI engine identifying and exploiting zero day vulnerabilities. Chaos cannot be far behind.
Take Action:
Red teams can try to use AI models using the above approach and identify vulnerabilities before they get out in the wild. Keep an eye out for more research in this space. See if they can build this system and



I'm a little skeptical about the “70% of organisations have a dedicated SaaS security teams”. too, but I'm a big believer in the value of supply chain risk assessments, and tailoring these appropriately when the vendor provides a SaaS product or service.