The Economist's Cybersecurity Reading List | John Oliver & Pig Butchering Scams
CyberInsights #132 - 5 Cybersecurity Books to Read | One cybersecurity video to watch
This edition is not about cyber incidents that occurred this week. It is about good media content for people who want to understand cyber. Two of my favourite publications released things on cyber that I feel everyone should read and watch. So, no news this time, but great content on cyber.
The Economist lists 5 books in their list on “What to read to understand..” series on Cybersecurity
A classic on cryptography makes the list interesting!

I’m a fan of “What to read to understand _____” series by the The Economist. I’ve found many an interesting book to read from their series over the years. The new list in the series is on “What to read to understand Cybersecurity”. It contains a few interesting names. [LINK]
I was most surprised by “The Code Book” by Simon Singh. [LINK]
The book was first published in 2000 and it was one of the books that got me fascinated by cryptography. Simon Singh, explains the basics of cryptography in a fun and fascinating way. I loved it so much that I went on to read other books by Simon Singh including “Big Bang” and “Fermat’s Last Theorem”. I can safely say that this book made me start loving cryptography.
There are 4 other books, covering varied topics - cybersecurity as a geopolitical issue, social engineering and even cryptocurrency crime lords. Read them all if you can!
Take Action:
If you are yet to firm up your reading list for the year, go ahead and add these books to your list. If you have not read “The Code Book”, I would highly recommend reading it.
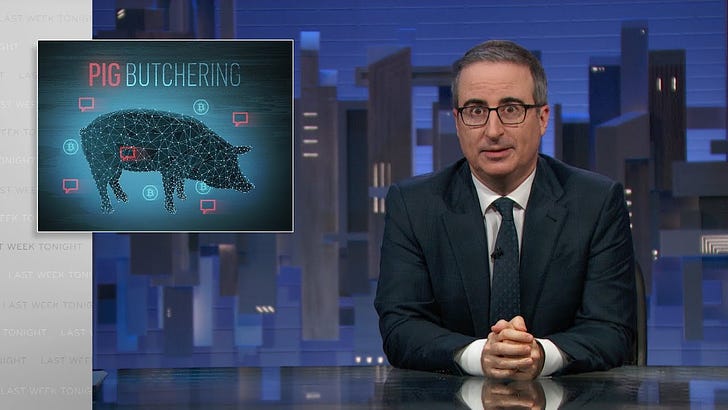
John Oliver and the Pig Butchering Scam
When a star like John Oliver talks about cybersecurity, it increases awareness
I have a t-shirt that says “I get my news from John Oliver”. It’s almost true. I love the research that John does on a topic.
In this video, he talks about the human aspect of pig butchering scams. I had written about pig butchering scams in this edition:
Pig butchering scams are sophisticated social engineering attacks. They typically start with an innocuous message, which appears to be misdirected. Something like “Did you get the tickets for tonight?”
The attacker then starts a conversation to build trust and can then get the victim to part with their money.
Take Action:
Watch this video and share it widely. This is one of the best ways to create awareness. If you can, get your tech team to open this URL and do screenings of this video in your office!
This scam impacts the elderly and the people who live alone more. Share this video with the elderly people in your circle of influence.